Signatures in WAF Policy
Overview
The final step in WAF processing is a signature check. Core Rule Sets (CRS) can be configured under the Signatures tab. You can configure to run custom rules before CRS or after CRS as well. This article shows how to configure pre-CRS, CRS, and post CRS rules.
Pre-CRS Rules
The custom rules that are applied before the supplied OWASP Core Rule Set (CRS) are called Pre-CRS rules.
To define Pre-CRS rules,
- From the Avi UI, navigate to Templates > WAF > WAF Policy and click on Create.
or
Edit an existing WAF Policy. - Enter the required details under the Settings tab.
- Click on the Signatures tab.
- Under Pre-CRS rules, click on Create Group.
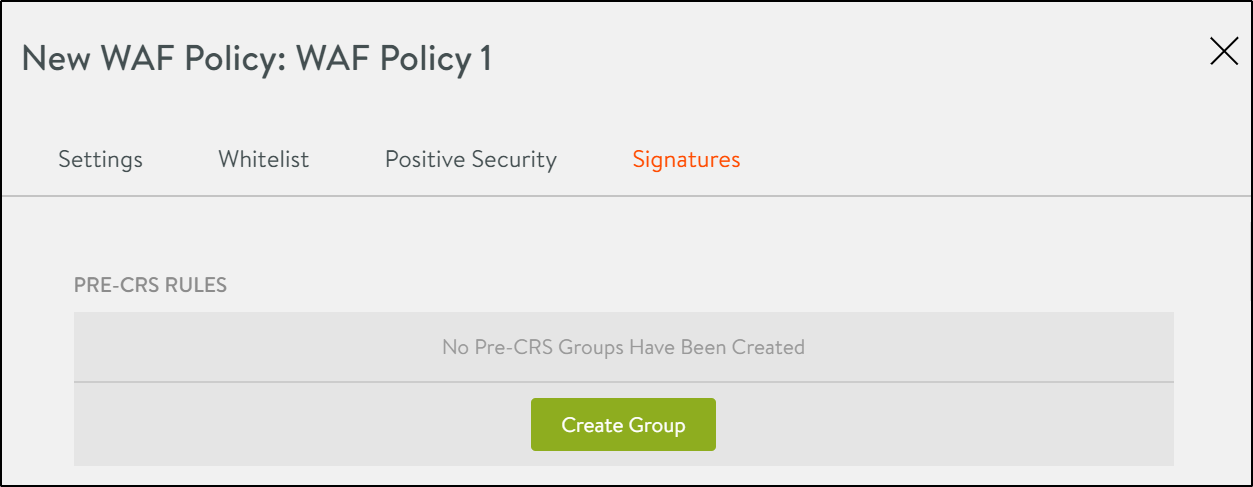
- Enter the Group Name. Every rule is configured within a group.
- Click on the Create Rule button.
- Enter a Name for the rule.
- Select a mode:
i) Policy Mode: When Detection or Enforcement can’t be applied, the policy mode is used. For the policy mode to take effect, the WAF Policy should allow delegation.
ii) Detection: WAF rules will be processed but HTTP transactions will not be intercepted. Any rule configured to intercept HTTP transactions will be bypassed.
iii) Enforcement Mode:WAF rules are processed and HTTP transactions intercepted, as per the rules configured. - Enter the Rule in the text box.
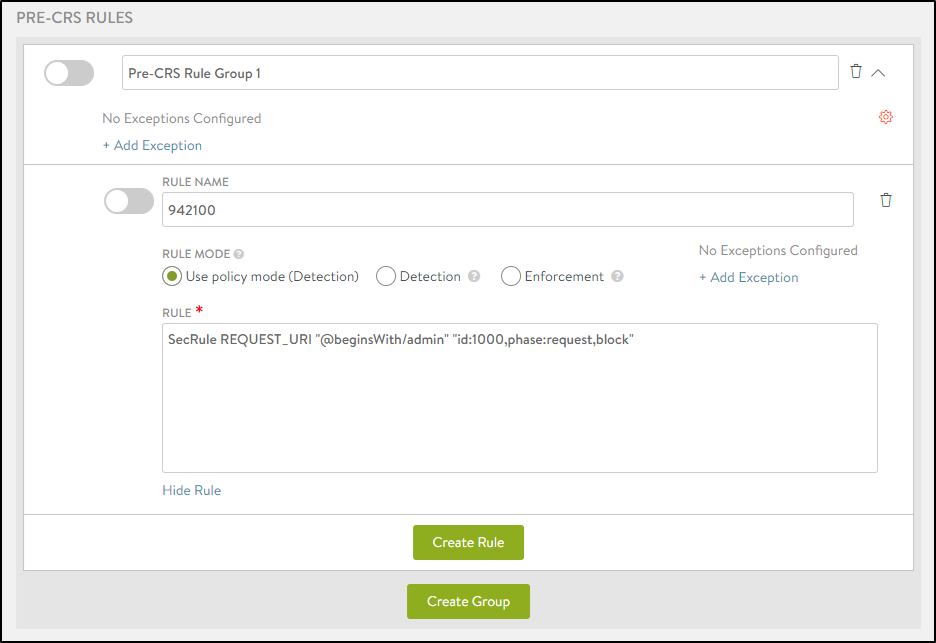
- Click on the Create Group button.
The Pre-CRS rule is listed as shown below:
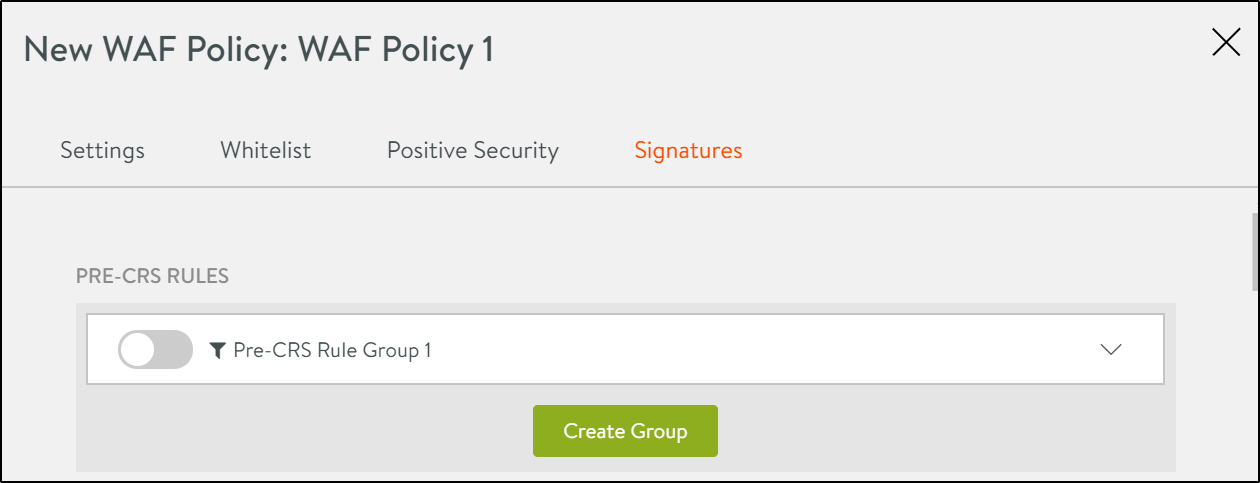
- Click on the toggle button to enable the rule.
Exceptions
Exceptions are a common way of tuning a WAF policy to work with an application. These are normally created when an application’s regular traffic matches specific WAF rules. The following are a few other reasons for creating exceptions are:
- For false-positive mitigation.
- For applications that do not conform with the System-WAF-Policy.
- For applications transmitting data that might appear like an attack. For instance, transferring HTML content in query parameters.
- For applications with special requirements that are not allowed in the policy. For instance, accessing application on its direct IP address.
- You can use Avi Vantage’s recommendation system to create exceptions or you can even add them manually.
To define an exception manually,
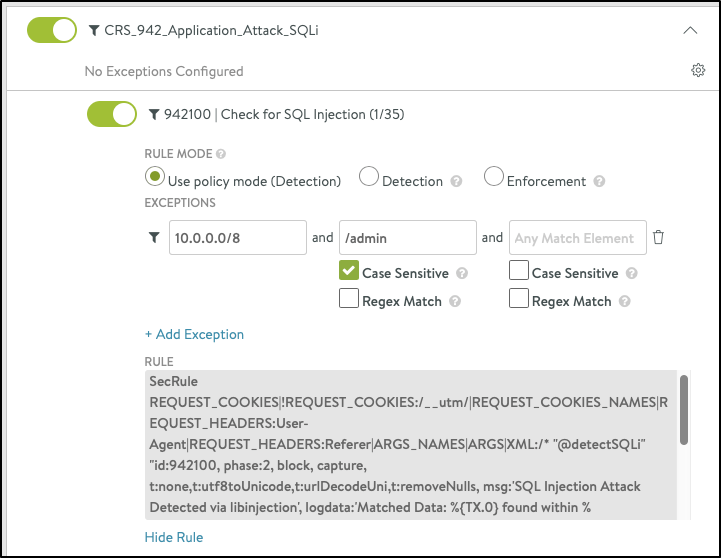
- Click on +Add Exception to manually configure exceptions. Click here to know more about exceptions.
- Configure exceptions for IP address/subnet, path, or any match element. For example, Subnet- 10.0.0.0/8, Path- /admin , Match Element - REQUEST_BODY.
-
Configure the following options for Path and Match Element, as required:
i) Case Sensitive - The case of the characters have to match to create an exception
ii) Regex Match - The pattern of the string of characters should match to create an exception.Note: Exceptions can be created on a group level or a rule level.
This is another example of where if there is match element like say ARGS:xyz, a request matching the IP and Path will just have ARGS:xyz removed while processing the rule.
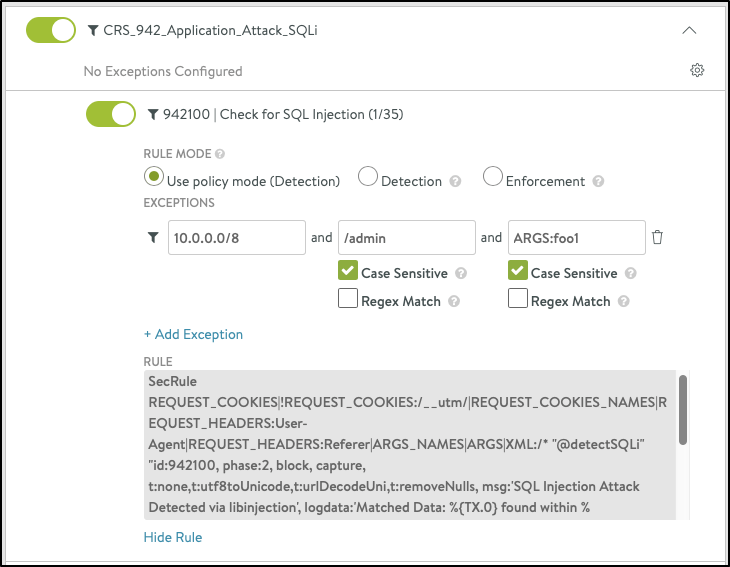
Here, the rule is processed, but ARGS:xyz is not used in running the rule.
Recommended Assisted Workflow
The following steps are for a recommended workflow to configure exceptions:
- Using WAF Log Analytics and find possible false-positives.
- False-positives may occur in large numbers and for different client IP addresses.
- To understand the context for false-positives, consult the application owner if possible.
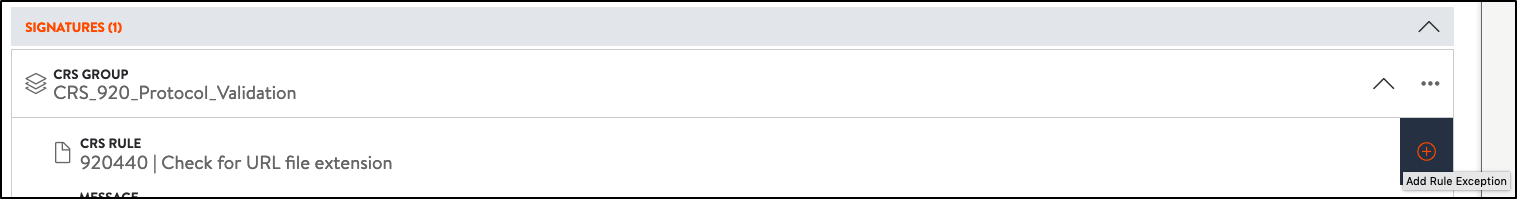
- In the log, choose the WAF hit entry that you want to add the exception for, and click on + Add Exception.
- The modal dialog will generate a set of suggested values.
- These values are pre-computed from the log entry and related findings.
- Save the exception to apply it to the policy.
CRS Rules
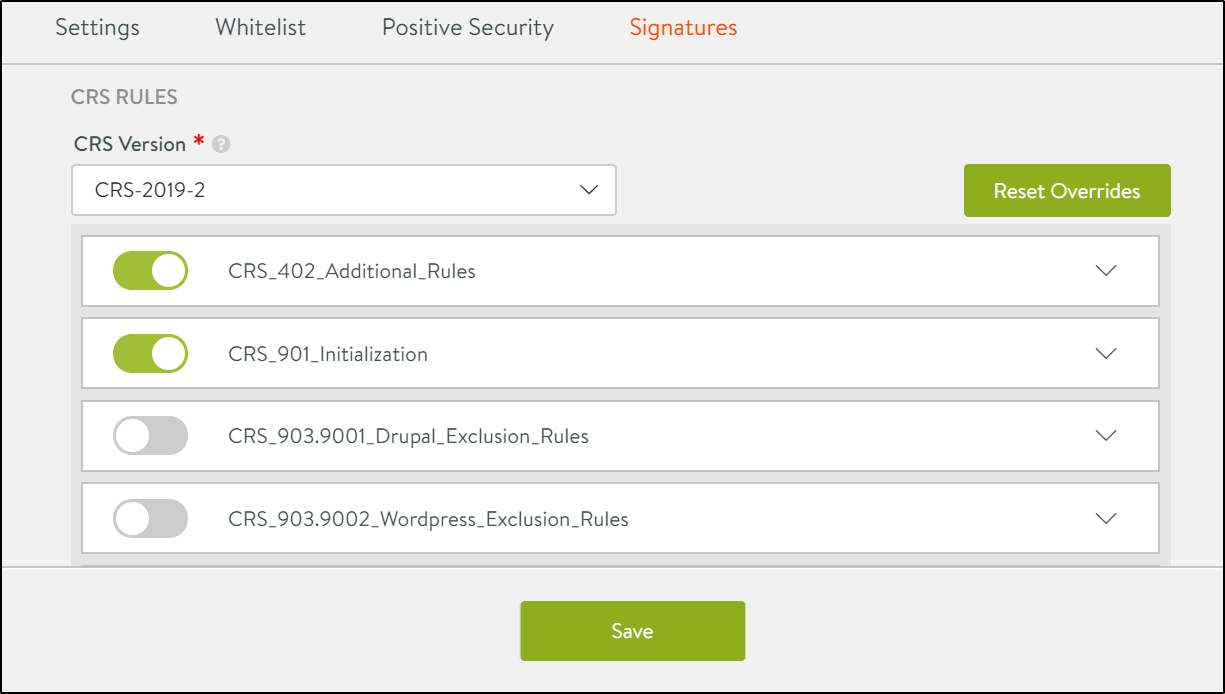
In this section CRS Rules the Avi supplied OWASP CRS policy can be configured. It covers the OWASP Top Ten attack protection.
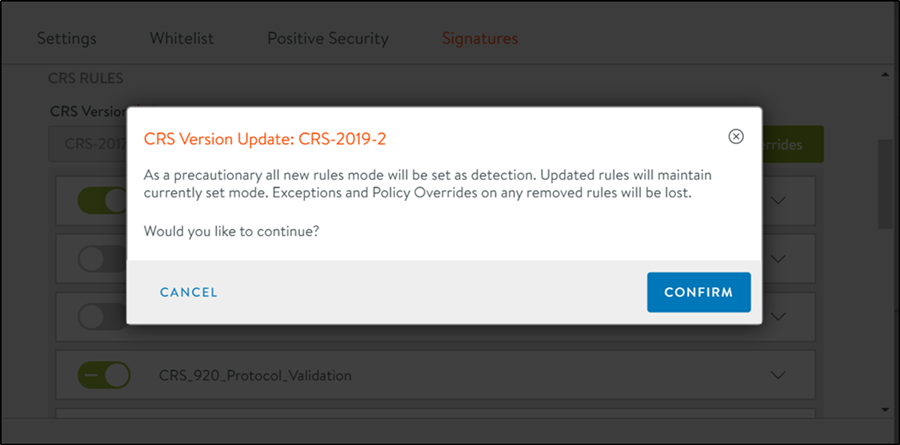
Note: If the CRS version is updated, all new CRS rules will be in Detection mode. With this, you can update the CRS ruleset without any risk in production. However, these new rules must be moved into Enforcement mode (or inherited policy mode) manually.
All updated rules will continue to remain in the same mode and the existing exclusions will be applied to the rules.
To update CRS Rules,
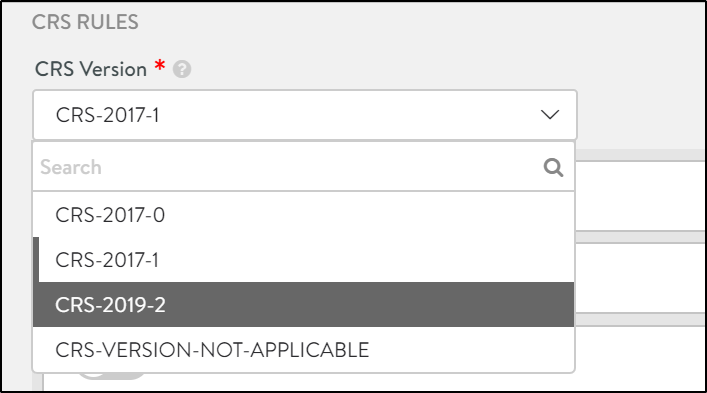
- Under the Signatures tab, scroll down to the CRS Rules section.
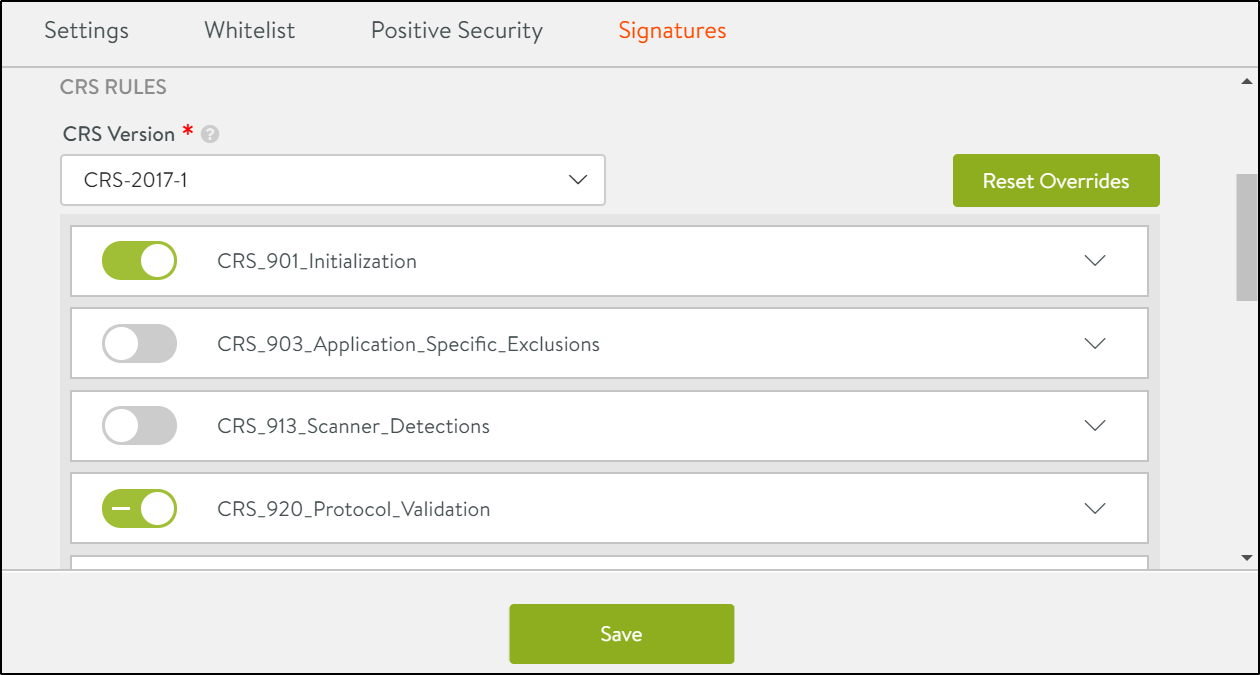
- Click on the required CRS Version to select it.
-
The change log is displayed as shown below. Click on Confirm to update the CRS version.
- Click on the toggle buttons to enable/disable a rule listed under the rule set.
- Click on Save to update the changes.
Post-CRS Rules
The custom rules that are applied after the supplied OWASP Core Rule Set (CRS) are configured under Post-CRS rules.
To configure post-CRS rules,
- Under the Signatures tab, scroll down to the Post-CRS Rules section.
- Create Groups and Rules as discussed in the Pre-CRS Rules section.
- Click on Save.