Tenants Versus SE Group Isolation
Overview
There are multiple ways to create isolation within Avi Vantage. This article explores the difference between tenants and SE groups and their relationship to data plane isolation and control plane isolation.
| Isolation | Tenant: Provider Context |
Tenant: Tenant Context |
SE Group |
| Control Plane | Yes | Yes | No |
| Data Plane | No | Yes | Yes |
Service Engine Groups
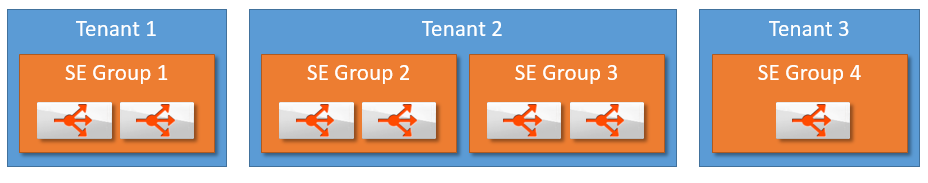
SE groups are an inherent method of grouping Service Engines to provide data plane isolation. A single tenant may have one or more SE groups. Multiple tenants may also point to one or more SE Groups. A virtual service may only be serviced by one SE group. If one of its SEs fail, another SE within the same SE group may take over. SEs in other SE groups may not be pulled in to provide capacity for another SE group. This ensures data plane isolation.
Examples
An administrator manages an application in both test and production environments. Each application’s virtual service should be deployed on a different SE group. For ease of management, both applications can be in the same tenant (tenant 2 in the image), though arguments could be made for separating these different environments into two separated tenants (such as tenant 1 and 3 in the image).
Example 2:
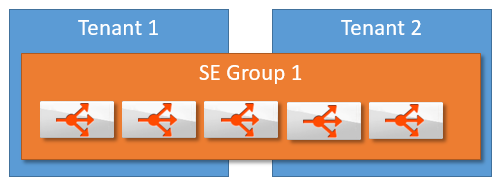 A cloud service provider manages multiple customer’s applications. Placing each customer in a unique tenant guarantees there will be complete configuration isolation. The service provider may choose to allow all tenants to have isolated Service Engines, or they may choose to place multiple tenants on the same SE group’s SEs to reduce idle resources.
A cloud service provider manages multiple customer’s applications. Placing each customer in a unique tenant guarantees there will be complete configuration isolation. The service provider may choose to allow all tenants to have isolated Service Engines, or they may choose to place multiple tenants on the same SE group’s SEs to reduce idle resources.
Tenants
A tenant is a logical grouping of configuration. An administrator may belong to one or multiple tenants, but may only view and edit one tenant at a time. Each tenant has its own isolated control plane configuration.
Each tenant may or may not have its own isolated data plane. This will depend on the global configuration of the Avi Vantage deployment.
Tenants may be deployed within a Provider Context or a Tenant Context:
- Provider Context mode: Service Engine groups are shared across tenants.
- Tenant Context mode: Service Engine groups are exclusive to each tenant
In Avi Vantage, Virtual Routing Forwarding (VRF) contexts can be created to isolate traffic within a system.
In VMware deployments, all networks are discovered by default under the admin tenant in the global VRF. The networks cannot be moved to another tenant. When creating tenants in vCenter deployments, the tenant_vrf flag for the tenant must be set to false, to allow VRFs to be shared across tenants. In order to ensure network isolation, the user must create additional VRFs within the admin tenant and then move networks into those VRFs. When creating a virtual service in the non-admin tenant, the user would select the corresponding VRF that was created in the admin tenant.
Configuring Tenant Settings
Via the Avi UI
To configure the tenant settings via the UI,
- Navigate to Administration > Settings > Tenant Settings.
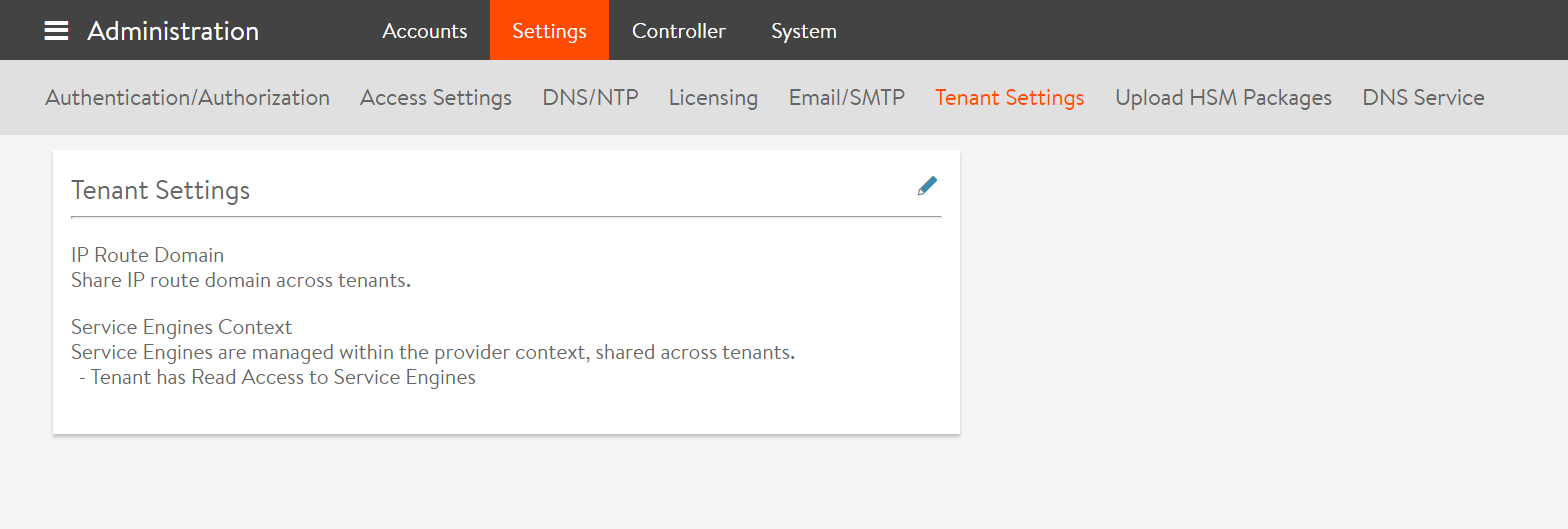
- Click on the Edit button.
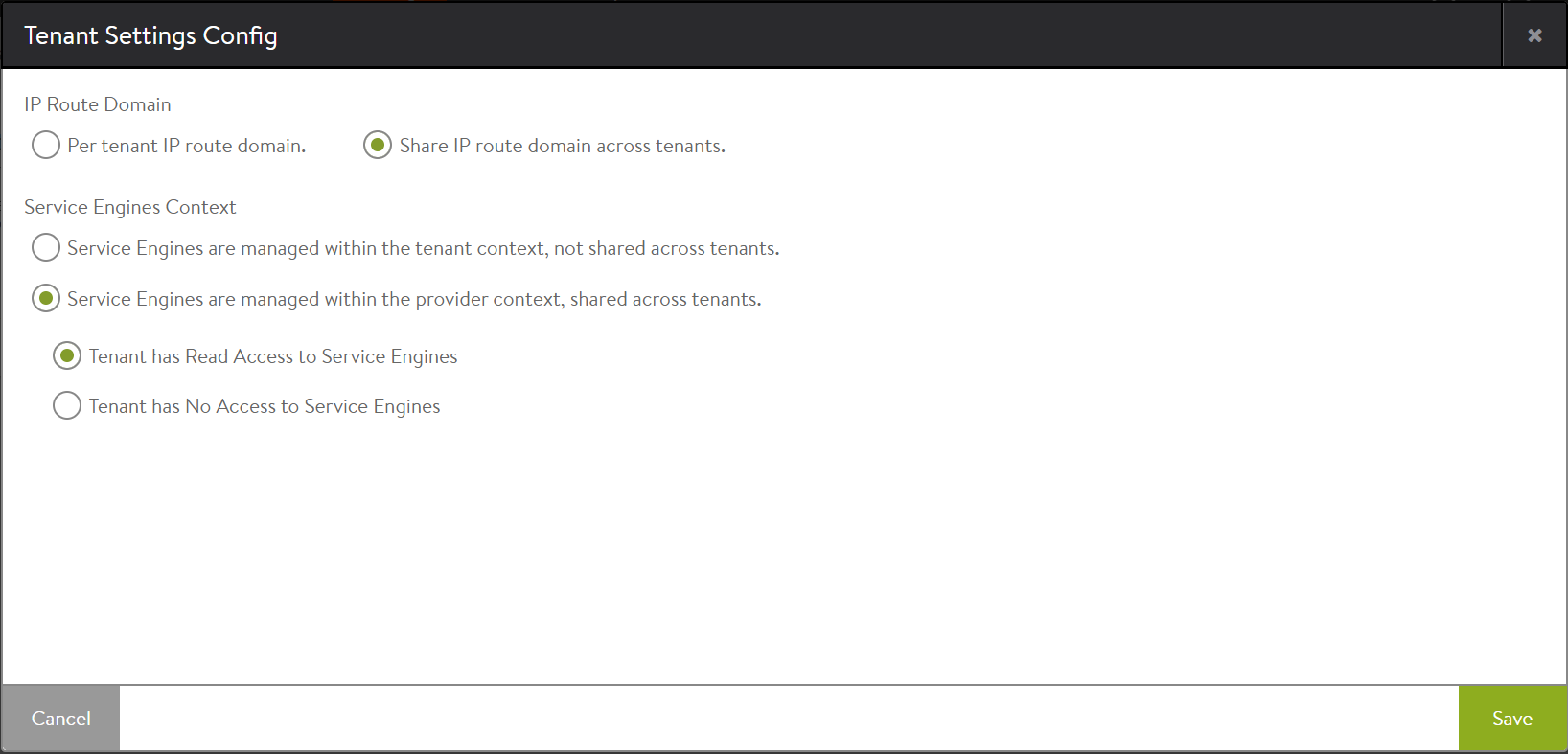
- To configure IP route domain per tenant select Per Tenant IP route domain, else select Share IP route Domain.
- Select the context mode as applicable:
- Service Engines are managed within the tenant context, not shared across tenants to enable the Tenant Context Mode.
- Service Engines are managed within the provider context, shared across tenants to enable the Provider Context Mode.
- In the provider context, enable read access to Service Engines, if required.
The Tenant Settings Config screen is as shown below:
- Click on Save.
Note: The configuration made via the UI will remain as the global configuration when creating a tenant. These values can be overridden for a specific tenant via the CLI or API.
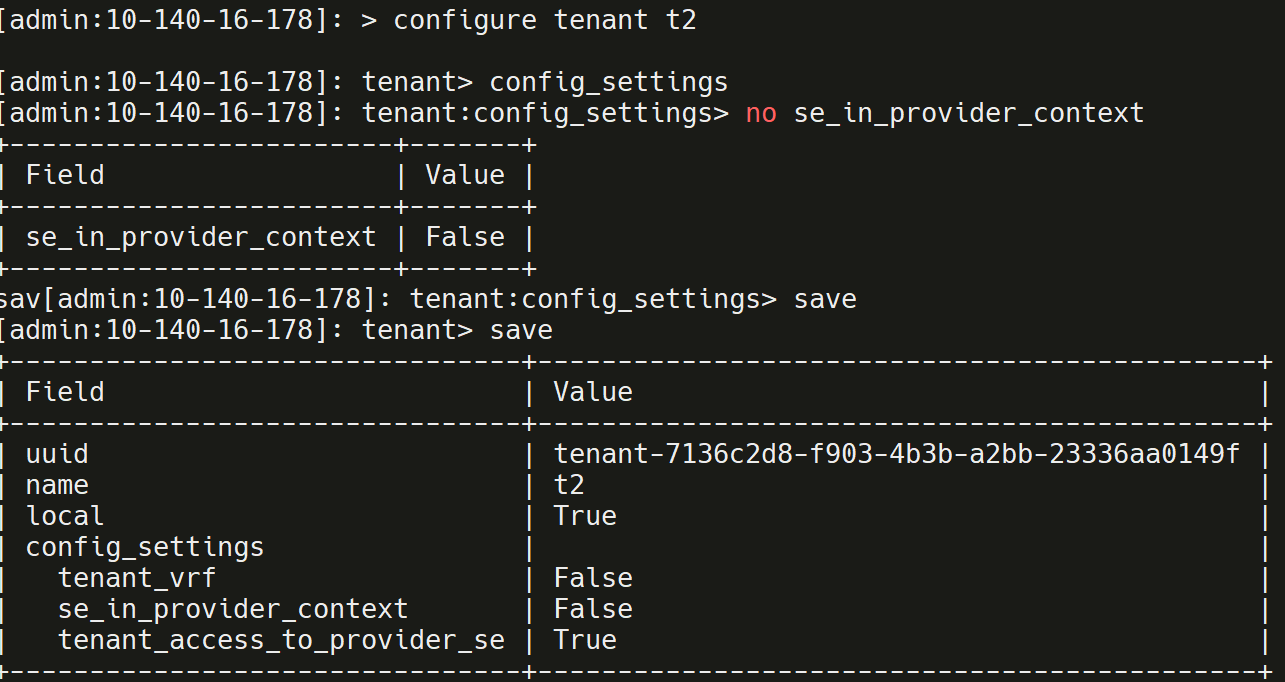
Via the CLI
Login to the shell and enter the configuration as shown below:
| Field | Value | Description |
|---|---|---|
| se_in_provider_context | True | Service Engines are managed within the provider context , shared across tenants |
| se_in_provider_context | False | Service Engines are managed within the tenant context , not shared across tenants |
| tenant_access_to_provider_se | True | Tenant has read access to Service Engines |
| tenant_access_to_provider_se | False | Tenant has no access to Service Engines |
| tenant_vrf | True | Configure IP route domain per tenant |
| tenant_vrf | False | Share IP route domain across tenants. For every tenant there is a different VRF. |
Note: In the global configuration, se_in_provider_context is set to True. However this can be changed for a tenant.