TCP SYN Flood Attack Protection on Avi Vantage
Overview
TCP SYN attack is a type of DDOS (distributed denial-of-service) attack in which the attacker makes use of the three-way TCP handshake process to attack the server. A huge number of TCP SYN requests are sent and when the server or the target device responds with SYN-ACK, there is no ACK response. Because of this, there are huge number of half-opened TCP connections. By repeatedly sending connection request (SYN) packets, the attacker is able to overwhelm all available ports on a targeted server machine, causing the targeted device to respond to legitimate traffic sluggishly or not at all.
TCP SYN Flood Attack Mitigation on Avi Vantage
Avi Vantage supports TCP SYN flood detection and mitigation without any user intervention. Prior to the Avi Vantage release 20.1.3, the synseen_entries_thresh parameter is used to assign a threshold value for the SYN packets. Once the synseen_entries_thresh is exceeded, new SYN packets are dropped resulting in denial of service of legitimate connection requests also. The calculation of synseen_entries_thresh is based on number of cores. In case of a large system, the synseen_entries thresh is above 1 million. In case a SYN attack happens, Avi Vantage looks up flow table or connection table before it starts dropping connection. Avi Vantage makes use of the various metric and events to detect TCY SYN attack. This is helpful in avoiding rejection or closure of the legitimate TCP connections or requests.
TCP Syn flood attack is mainly aimed at memory resource exhaustion. Each SYN packet will result in allocation of memory to keep the state of the embryonic connections. Avi Vantage mitigates Syn flood using a solution based on SYN cookies. Once the number of embryonic connections exceed a limit, TCP/IP stack or other components stop allocating memory till a connection is fully established. The limit is available as a configurable flow_table_new_syn_max_entries under the Service Engine group properties. The default value for the flow_table_new_syn_max_entries parameter is 40000.
Metrics and Events
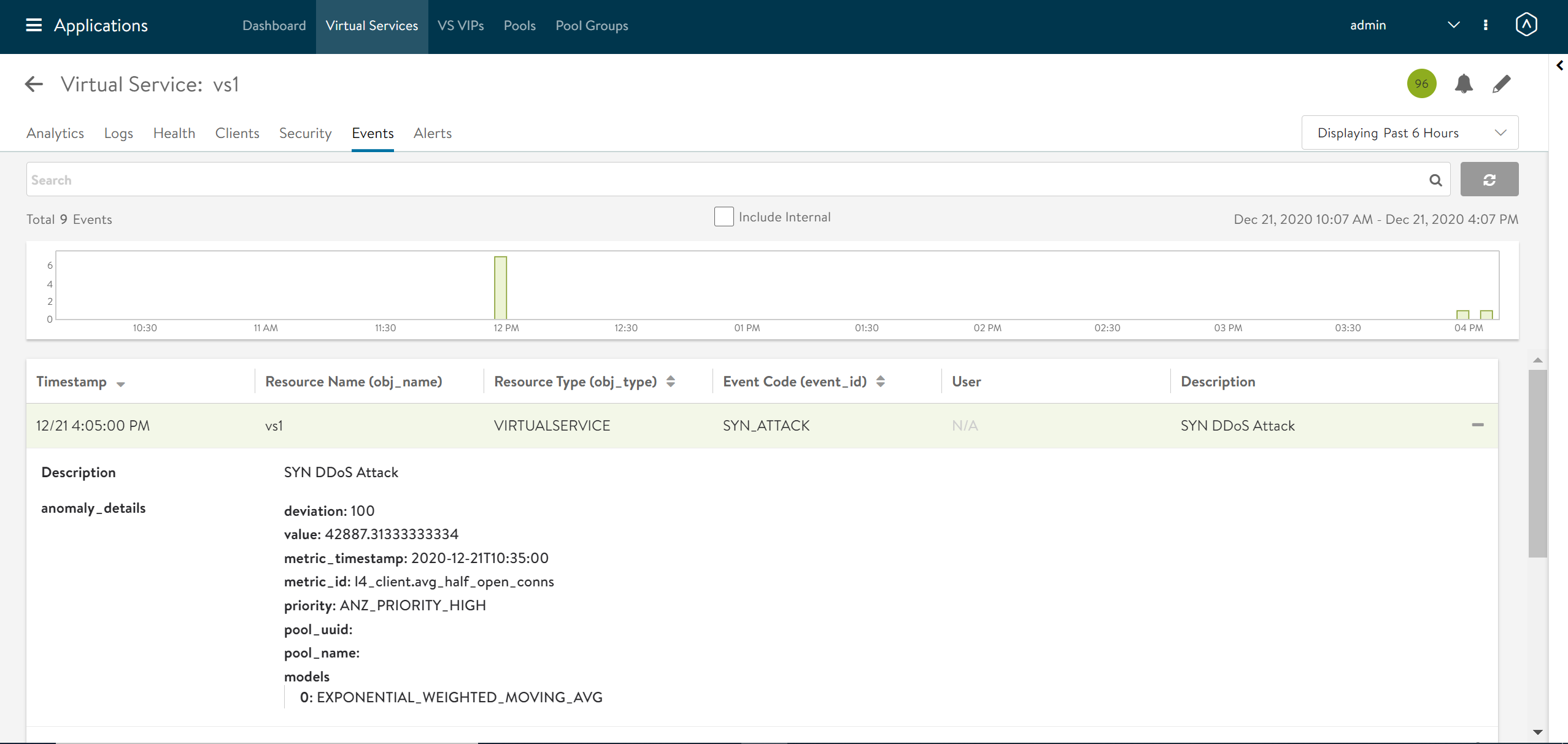
When a TCP SYN Attack is detected, Avi Vantage generates logs related to the TCP SYN Attack for the same. Navigate to Applications > Virtual Service , and select the Events tab to check the events related to TCP SYN Attack for the specific virtual service. The following screenshot shows the virtual service vs1 is under TCP SYN Attack.
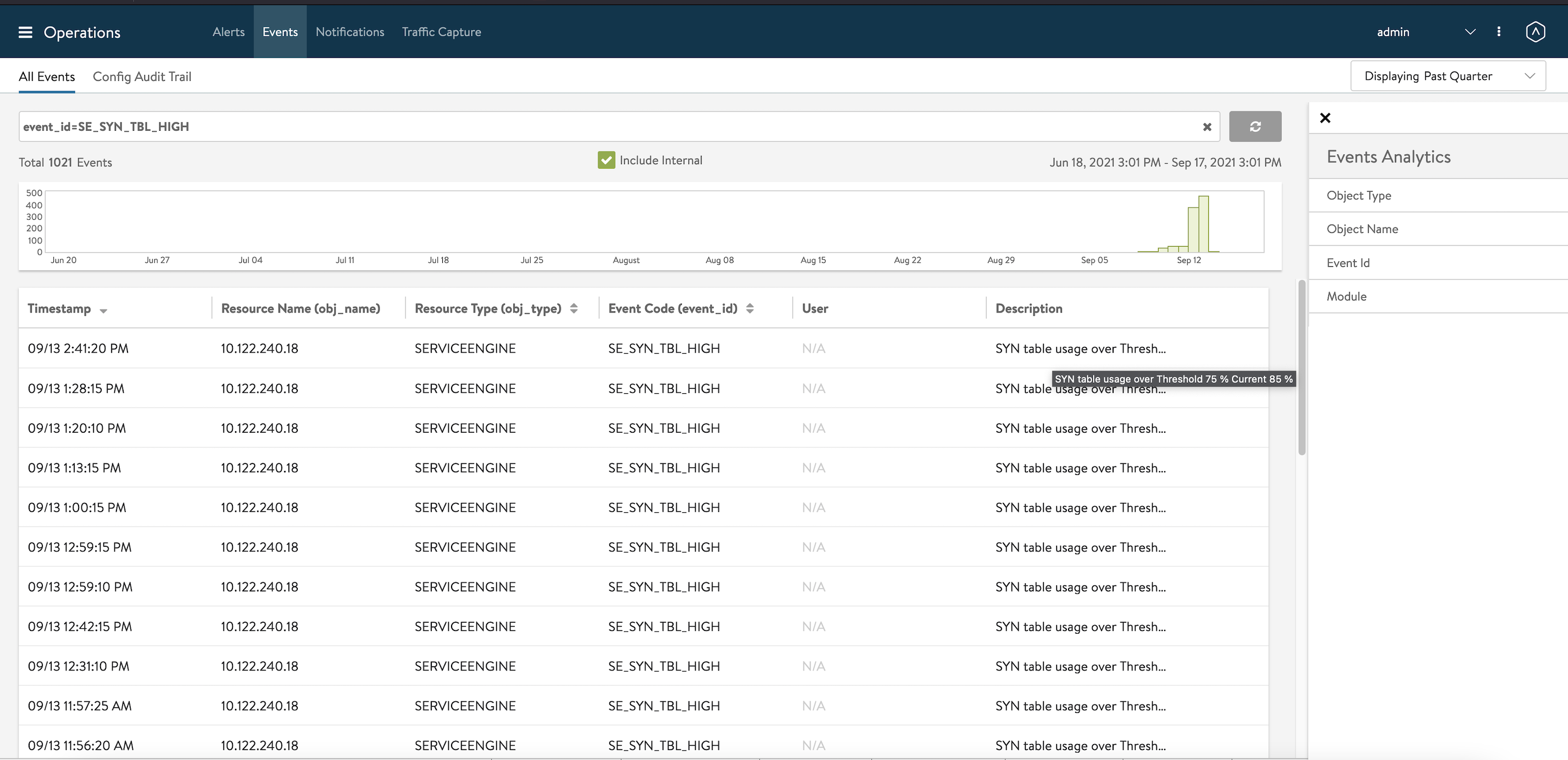
SE_SYN_TBL_HIGH Alert
When SE Limits are breached for total SYN that can be in TCP SYN FLOOD traffic, the Controller will display an alert message as SE_SYN_TBL_HIGH.