SSL/TLS Profile
Overview
This guide explains the SSL/TLS profile details.
SSL/ TLS Profile
Avi Vantage supports the ability to terminate SSL connections between the client and the virtual service, and to enable encryption between Avi Vantage and the back-end servers. The Templates > Security > SSL/TLS Profile contains the list of accepted SSL versions and the prioritized list of SSL ciphers. To terminate client SSL connections, both an SSL profile and an SSL certificate must be assigned to the virtual service. To also encrypt traffic between Avi Vantage and the servers, an SSL profile must be assigned to the pool. When creating a new virtual service via the basic mode, the default system SSL profile is automatically used.
Each SSL profile contains default groupings of supported SSL ciphers and versions that may be used with RSA or an elliptic curve certificates, or both. Ensure that any new profile created includes ciphers that are appropriate for the certificate type that will be used. The default SSL profile included with Avi Vantage is optimized for security, rather than just prioritizing the fastest ciphers.
Creating a new SSL/TLS profile or using an existing profile entails various trade-offs between security, compatibility, and computational expense. For example, increasing the list of accepted ciphers and SSL versions increases the compatibility with clients, while also potentially lowering security.
Notes:
- Starting with Avi Vantage version 18.2.3, Avi Vantage can accommodate a broader set of security needs within a client community by associating multiple SSL profiles with a single virtual service, and have the Service Engines choose which to use based on the client’s IP address. For more information, refer to the Client-IP-based SSL Profiles article.
- Starting with Avi Vantage version 18.2.6, Avi Vantage supports TLS 1.3.
- Starting with Avi Vantage version 20.1.1, the virtual service creation without SSL profile should default to System-Standard-PFS SSL profile.
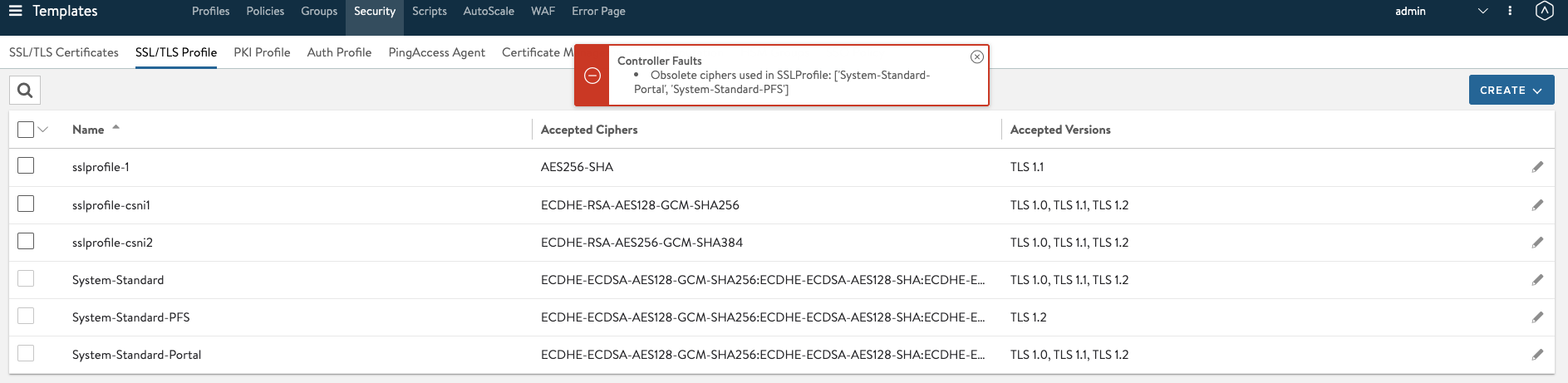
- Selecting unsafe ciphers will display the following error message.
SSL Profile Templates
To view the currently defined SSL and TLS profiles, navigate to Templates > Security and click to the SSL/TLS Profile tab.
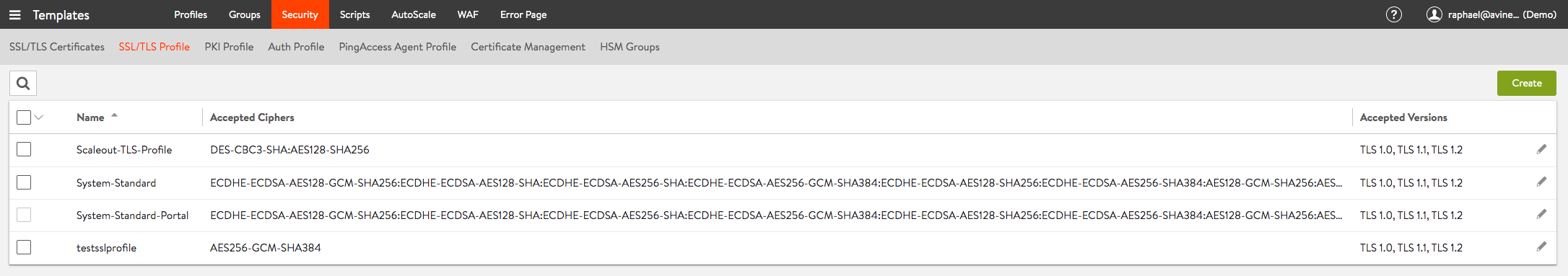
The table provides the following information for each SSL/TLS profile:
- Name — Name of the profile.
- Accepted Ciphers — List of ciphers accepted by the profile, including the prioritized order.
- Accepted Versions — SSL and TLS versions accepted by the profile.
Create an SSL/TLS Profile
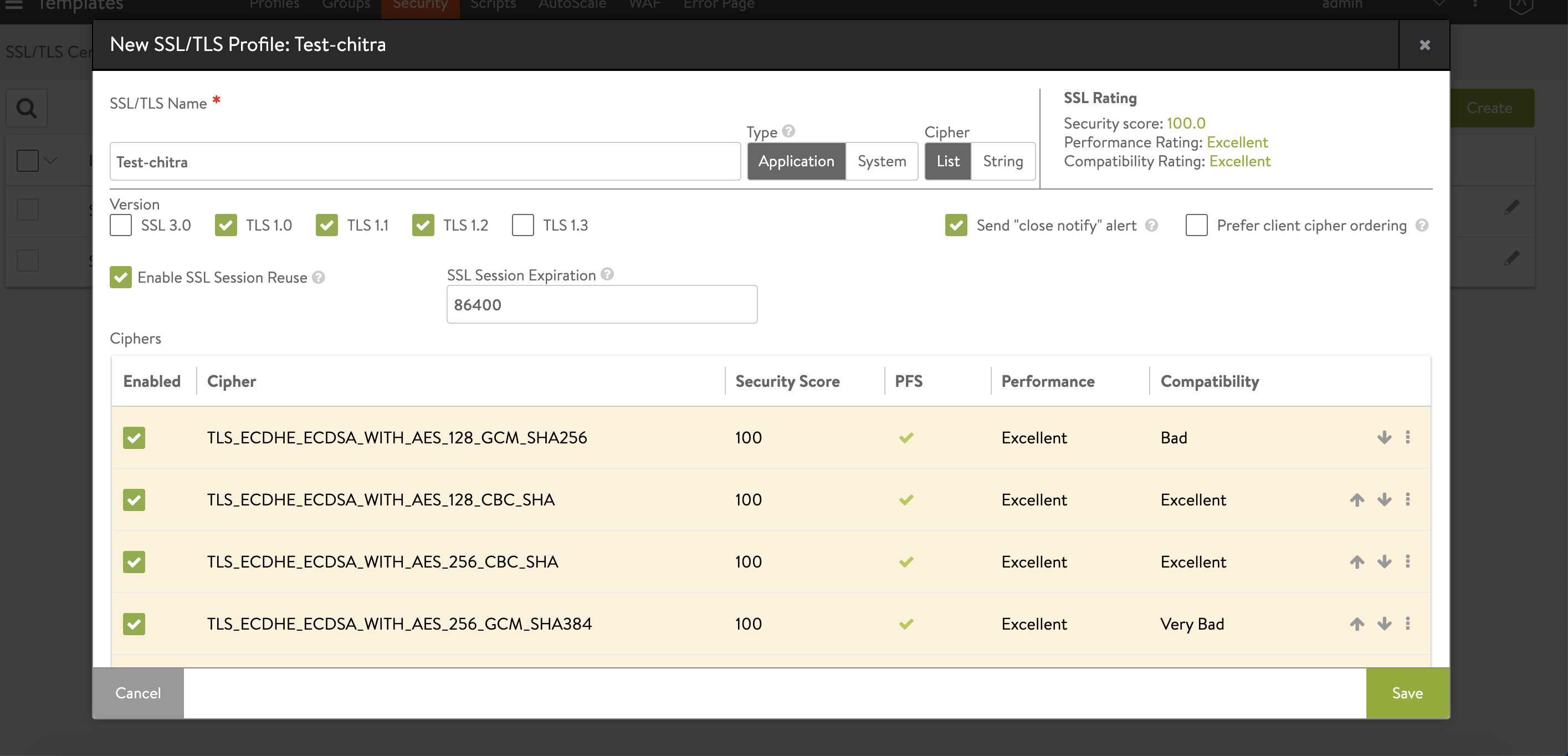
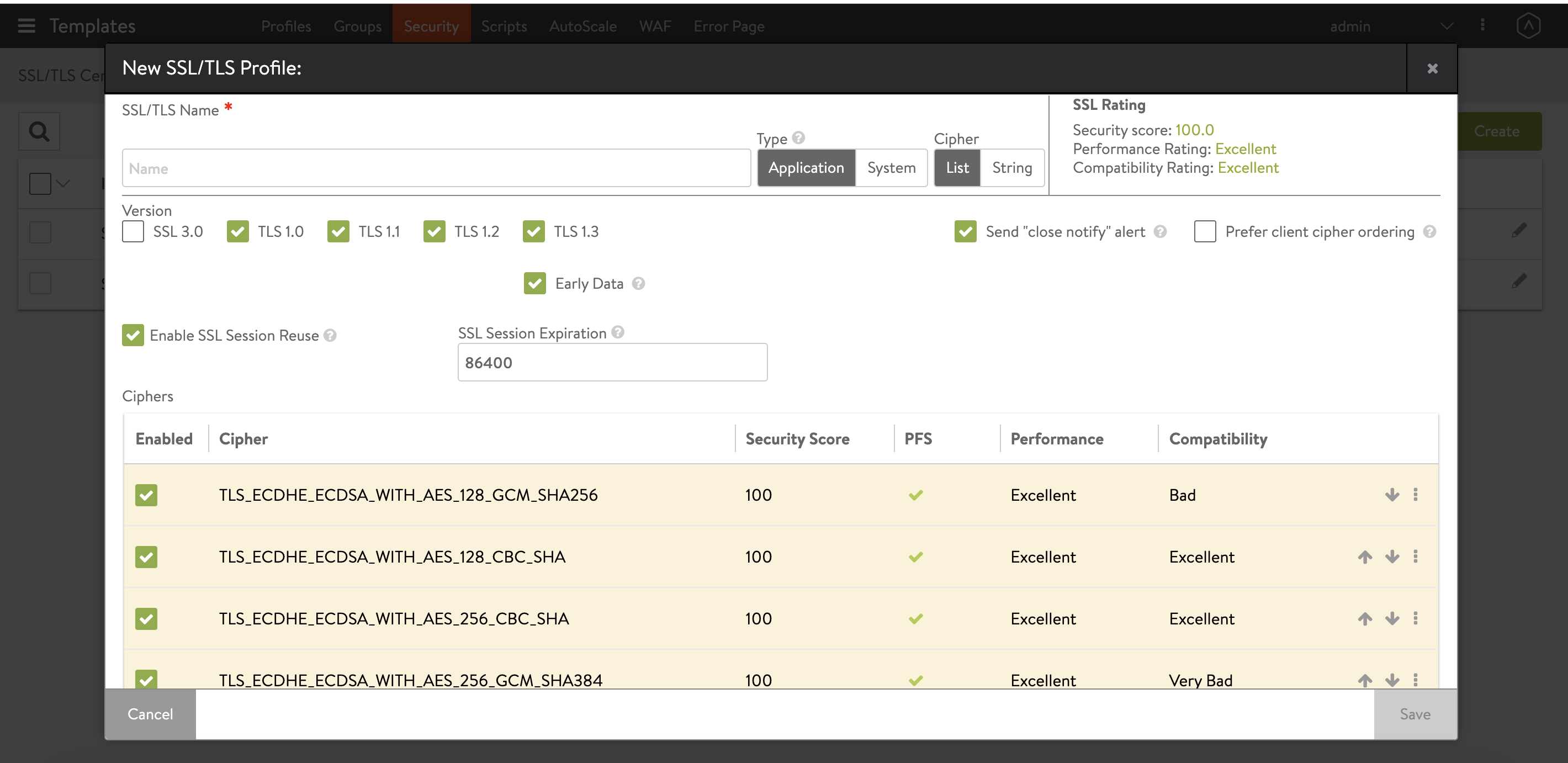
To create or edit an SSL profile, click on Create to see a window such as depicted in the below screenshots. In this, TLS1.3 is unchecked.
Checking the TLS 1.3 option causes the Early Data option to appear.
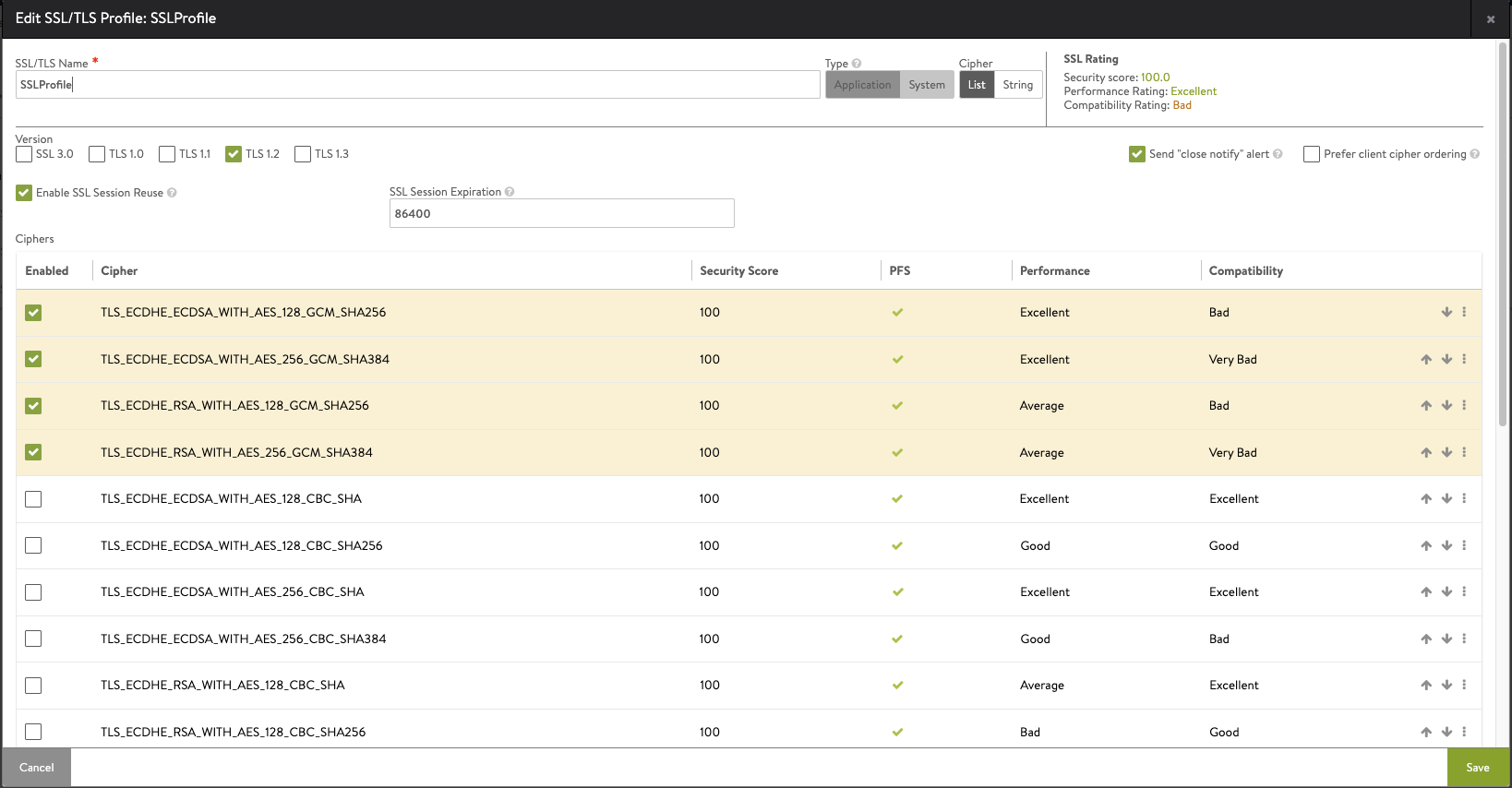
Checking TLS 1.2 option, the following ciphers are enabled:
Note: All cipher listed in both System-Standard and System-Standard-PFS SSL profiles are supported in both FIPS and non-FIPS modes of operation. The only exception is 3DES and TLS1.3 ciphers, since the FIPS stack does not support the TLS1.3 protocol.
UI Fields
- SSL/TLS Name — Specify a unique name for the SSL/TLS profile.
- Type — Choose Application if the profile is to be associated with a virtual service, System if the profile is to be associated with the Controller.
- Cipher — Ciphers may be chosen from the default List view or a String. The String view is for compatibility with OpenSSL-formatted cipher strings. When using String view, Avi Vantage does not provide an SSL rating, nor a score for the selected ciphers.
- SSL Rating — This is a simple rollup of the security, compatibility, and performance of the ciphers chosen from the list. Often ciphers may have great performance but very low security. The SSL rating attempts to provide some insight into the outcome of the selected ciphers. Avi Networks may change the score of certain ciphers from time to time, as new vulnerabilities are discovered. This does not impact or change an existing Avi Vantage deployment, but it does mean the score for the profile, and potentially the security penalty of a virtual service, may change to reflect the new information.
- Version — Avi Vantage supports versions SSL 3.0, TLS 1.0 and newer. The older SSL 2.0 protocol is no longer supported.
Starting with release 18.2.6, TLS 1.3 protocol is supported. Users must select one or more of the three supported TLS 1.3 ciphers in the list of ciphers or configure them in the Ciphersuites option under the String view. - Send “close notify” alert — Gracefully inform the client of the closure of an SSL session. This is similar to TCP doing a FIN/ACK rather than an RST.
- Prefer client cipher ordering — Off by default, set this to On if you prefer the client’s ordering.
- Enable SSL Session Reuse — On by default, this option persists a client’s SSL session across TCP connections after the first occurs.
- SSL Session Expiration — Set the length of time in seconds before an SSL session expires.
- Ciphers — When negotiating ciphers with the client, Avi Vantage will give preference to ciphers in the order listed. The default cipher list prioritizes elliptic curve with PFS, followed by less secure, non-PFS and slow RSA-based ciphers. Enable, disable, and reorder the ciphers via the List view. In the String view, manually enter the cipher strings via the OpenSSL format, which is documented on the OpenSSl.org website. You may use an SSL/TLS profile with both an RSA and an elliptic curve certificate. These two types of certificates can use different types of ciphers, so it is important to incorporate ciphers for both types in the profile if both types of certs may be used. As with all security, Avi Networks recommends diligence to understand the dynamic nature of security and to ensure that Avi Vantage is always up to date.
- Ciphersuites — Starting with Avi Vantage 18.2.6, this option exclusively configures TLS 1.3 protocol ciphers. Currently, Avi supports
TLS_AES_128_GCM_SHA256TLS_AES_256_GCM_SHA384TLS_CHACHA20_POLY1305_SHA256
Note: These ciphers will only work with the TLS 1.3 protocol. The old ciphersuites cannot be used with the TLS 1.3 protocol.
- Early Data — Starting with Avi Vantage 18.2.6, this option enables TLS-v1.3-terminated applications to send application data (referred to here as early data or 0-RTT data) without having to first wait for the TLS handshake to complete. This saves one full round-trip time between the client and server before the client requests can be processed. SSL session reuse must be enabled to use the Early Data option.
Note: Starting with Avi Vantage 21.1, Avi Vantage supports configuring Elliptic Curve Cryptography (ECC) Cipher Suites in SSL profile.
Signature Algorithms
The SSL client uses the “signature_algorithms” extension to indicate to the server which signature/hash algorithm pairs may be used in digital signatures.
The extension_data field of this extension contains a supported_signature_algorithms value.
Supported Hash Algorithms:
- md(5)
- sha1(2)
- sha224(3)
- sha256(4)
- sha384(5)
- sha512(6)
Supported Signature Algorithms:
- rsa
- dsa
- ecdsa
In Avi Vantage the signature algorithms set by a client are used directly in the supported signature algorithm in the client hello message.
The supported signature algorithms set by a server are not sent to the client but are used to determine the set of shared signature algorithms and their order.
The client authentication signature algorithms set by a server are sent in a certificate request message if client authentication is enabled, otherwise they are unused. Similarly client authentication signature algorithms set by a client are used to determine the set of client authentication shared signature algorithms.
Signature algorithms will neither be advertised nor used if the security level prohibits them.
Configuring Signature Algorithm
The field signature_algorithm is introduced in the SSL profile configuration. By default, this field is set to auto.
show sslprofile System-Standard
[admin]: > show sslprofile System-Standard
+-------------------------------+----------------------------------------------------------------------------------+
| Field | Value |
+-------------------------------+----------------------------------------------------------------------------------+
| uuid | sslprofile-9052601e-0203-4702-81fd-221d0f4a3c5a |
| name | System-Standard |
| accepted_versions[1] | |
| type | SSL_VERSION_TLS1 |
| accepted_versions[2] | |
| type | SSL_VERSION_TLS1_1 |
| accepted_versions[3] | |
| type | SSL_VERSION_TLS1_2 |
| accepted_ciphers | ECDHE-ECDSA-AES128-GCM-SHA256:ECDHE-ECDSA-AES128-SHA:ECDHE-ECDSA-AES256-SHA:ECDH |
| | E-ECDSA-AES256-GCM-SHA384:ECDHE-ECDSA-AES128-SHA256:ECDHE-ECDSA-AES256-SHA384:EC |
| | DHE-RSA-AES128-GCM-SHA256:ECDHE-RSA-AES128-SHA:ECDHE-RSA-AES128-SHA256:ECDHE-RSA |
| | -AES256-SHA:ECDHE-RSA-AES256-SHA384:AES128-GCM-SHA256:AES256-GCM-SHA384:AES128-S |
| | HA256:AES256-SHA256:AES128-SHA:AES256-SHA:DES-CBC3-SHA |
| --------------------Truncated Output---------------------- |
| | |
| prefer_client_cipher_ordering | False |
| enable_ssl_session_reuse | True |
| ssl_session_timeout | 86400 sec |
| type | SSL_PROFILE_TYPE_APPLICATION |
| ciphersuites | TLS_AES_256_GCM_SHA384:TLS_CHACHA20_POLY1305_SHA256:TLS_AES_128_GCM_SHA256 |
| enable_early_data | False |
| ec_named_curve | auto |
| signature_algorithm | auto |
| tenant_ref | admin |
+-------------------------------+----------------------------------------------------------------------------------+
By default, Avi Vantage supports ECDSA+SHA256:RSA+SHA256 (when signature_algorithm is set to auto ).
Modify the signature algorithm as shown below:
> configure sslprofile System-Standard
sslprofile> signature_algorithm ECDSA+SHA256:RSA+SHA256:RSA-PSS+SHA256
Overwriting the previously entered value for signature_algorithm
sslprofile> save
Document Revision History
| Date | Change Summary |
|---|---|
| August 06, 2021 | Updated the support for Signature Algorithms |
| December 23, 2020 | Added note on System-Standard-PFS SSL profile |