Bot Attack Definition
A bot is a small software program designed to automate web requests based on specific user goals. Users deploy bots to perform a range of tasks without human intervention. Some of these are positive tasks, including customer service and fraud detection. However, others are malicious, such as scanning or scraping website content.
Tasks bots can run are generally simple and can be performed far more rapidly than typical human online activity. However, speed alone does not signal bot intent.
Some bots such as Googlebot are legitimate, used to crawl and index the web for search. But other bots are malicious, deployed to scan websites automatically for software vulnerabilities.
So although bots are neutral and can be used in both harmful and helpful ways, the phrase “bot attack” clearly has the negative connotation of an attacker with bad bots and a malicious goal.
Generally speaking, a bot attack defrauds, manipulates, or disrupts end-users of an application, website, API using automated web requests. The first simple spamming operations that made up automated bot attacks have today blossomed into complex criminal enterprises with massive infrastructures and economies that span continents.

Bot Attack FAQs
What is a Bot Attack?
What are bot attacks? Automated bot attacks range from lone hackers to massive cyber criminal organizations. More sophisticated attackers develop their own custom code and bad bots designed to circumvent application security monitoring.
Here are some common types of bots:
Botkits. For less sophisticated hackers, botkits are freely available on the Dark Web. Sellers of botkits offer paid executions of bot attacks, including DDoS attack bot software.
Botnets. A botnet, a portmanteau for robot network, is a group of interconnected machines working together to quickly complete tasks that are repetitive. A malicious botnet is a group of machines infected by malware and controlled by bot-herders or threat actors who launch coordinated, high volume DDoS bot attacks from a central point. Hackers deploy botnets most often for account takeover (ATO) attacks, credit card fraud, distributed denial of service (DDoS) attacks, and content scraping.
Spider bots. Spider bots, also called web crawlers or spiders, follow hyperlinks to browse the web to retrieve and index web content. Spiders download HTML and other resources, including JavaScript, CSS, and images, to process website content.
Scraper bots. Scraper bots read and save data from websites for reuse. For example, they may scrape specific data points such as product prices on eCommerce sites. Web scraping can violate terms of use and intellectual property laws, or even collect sensitive information.
Spam bots. A spam bot is designed to collect email addresses from websites, social media platforms, and organizations for spam mailing lists. A spam bot can then sell or use their list of email addresses for not only spam mail, but to gain unauthorized access to accounts via credential cracking—pairing up commonly-used passwords with your emails.
Social media bots. These bots operate on social media networks to generate posts and messages automatically, advocate positions, and gain followers. These bots can also engage in social engineering techniques to help their users with phishing schemes and other attacks.
Download bots. Download bots automatically download mobile apps or software to influence download statistics on popular app stores and ratings charts. They can also be used to create fake downloads as part of an application-layer Denial of Service (DoS) attack on download sites.
Ticketing bots. Ticketing bots purchase tickets to popular events automatically so scalpers can resell them for a profit.
Types of Botnet Attacks
Bots execute user attacks against APIs and web applications in order to alter or steal critical data. Various bots attack in different ways:
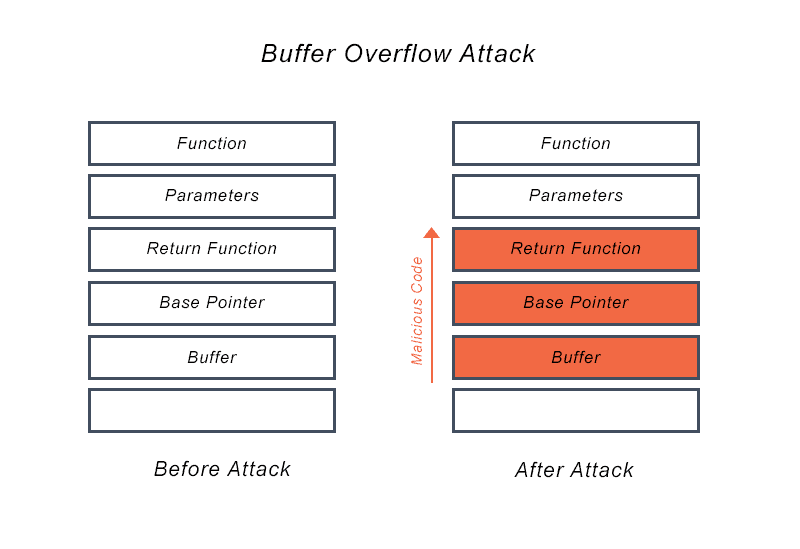
Distributed denial of service (DDoS) attacks. To launch this sort of attack, hackers deploy a botnet, a collection of hijacked internet-connected devices (internet of things or IoT devices). Each device can be surreptitiously controlled remotely to carry out DDoS attacks because it has been injected with malware without the knowledge. DDoS attacks target the top layer or the application layer—layer 7 of the OSI model. The attack works by flooding the server with excessive traffic until it can’t respond. DDoS protection is central to preventing bot attacks.
Web content scraping/web scraping bots. Web scraping bots are often disguised as web crawlers. But legitimate search engine bots from Google or Bing use googlebot, robots.txt, and other user agent strings to declare themselves and have improving end-user search engine results as their primary goal. Web scrapers scrape data automatically from other websites, to steal content.
Account takeover (ATO). These fraud attacks (also called credential stuffing) see attackers using automated bots for account takeover, locking out legitimate users and stealing personally identifiable information (PII).
Brute force attacks. A hacker launches a brute force attack by using trial-and-error to guess all possible combinations for encryption keys, login info, or a hidden web page. The brute-force attacker checks all possible passwords systematically until they find the correct response.
How to Prevent Bot Attacks?
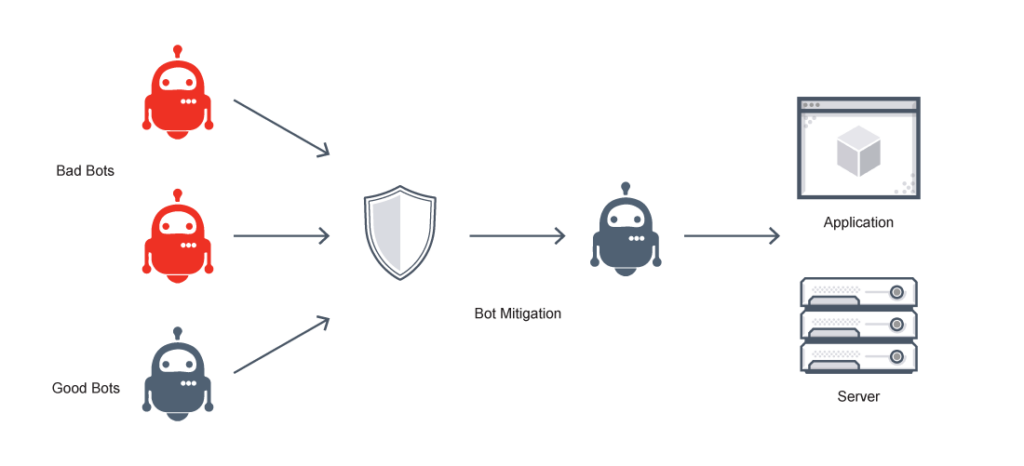
Effective bot attack protection requires the ability to identify bot attacks and take appropriate action based on accurate, relevant data.
Identify bot attacks. Establish a normal behavior threshold and identify problematic requests. Attack indicators vary between organizations. For example, suspicious activity indicators for a social media app login page include creation of multiple accounts from one IP address, password resets, and large-scale trends in login attempts.
Take appropriate action. Establishing a baseline enables distinguishing legitimate users from malicious actors. Appropriate corrective actions include ongoing observation, allowing, blocking, or alerting.
Display actionable, real-time bot management data. Organizations need a method to collect and visualize all web request data, metadata, and behavioral data within a unified console such as a web application firewall (WAF). This kind of granular visibility is central to an automated bot attack strategy.
Other, specific bot management solutions include:
Device fingerprinting. Device fingerprinting combines details from the user’s device and browser to track who and what is connecting. Bad bots must make multiple attempts with the same devices, which allows fingerprinting technologies to identify many fraud attempts.
Multi-factor authentication. MFA does not prevent bot attacks, but it makes them more difficult.
Browser validation. Browser validation verifies that the correct browsers are running, that the data is the right format, and that no unexpected JavaScript agents are present, for example.
Machine learning behavior analysis. Human users visiting websites typically exhibit certain behavior patterns, and bots behave in notably different ways. Behavioral analysis technology can help analyze user behavior and detect anomalies to identify bad bots.
Progressive challenges. Progressive testing to minimize disruption to real users might include: a cookie challenge, CAPTCHA, or JavaScript challenge.
Does VMware NSX Advanced Load Balancer Offer Bot Attack Prevention?
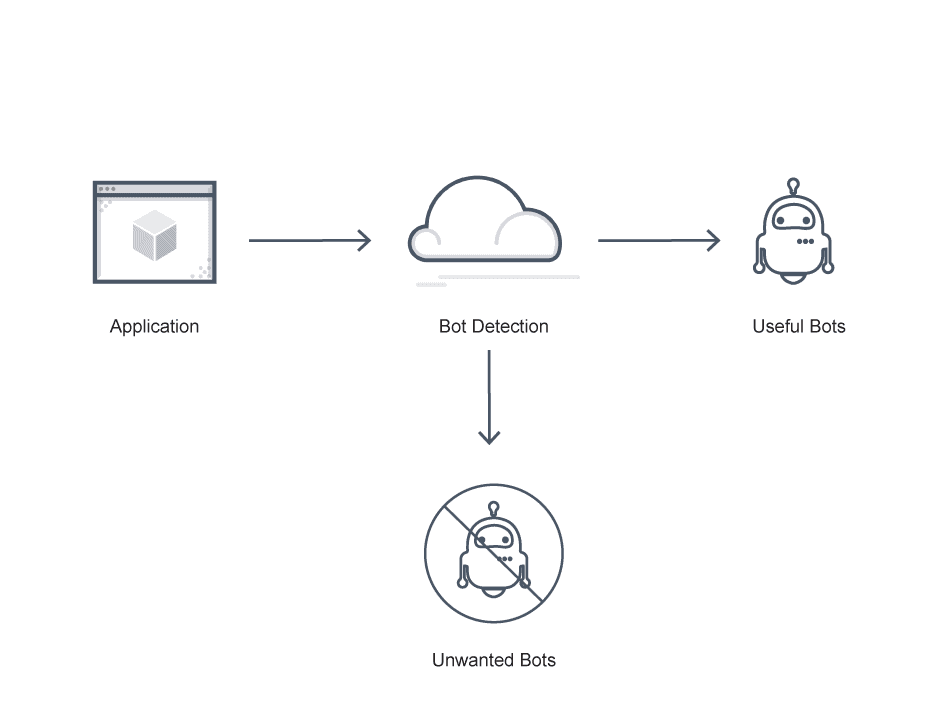
About half of all online traffic originates with bots. Managing this bot traffic is essential, because both malicious and helpful bot traffic exists.
The VMware NSX Advanced Load Balancer delivers software load balancers, container ingress, and web application firewall services to keep applications available, secure, and responsive. The VMware NSX Advanced Load Balancer natively mitigates against dozens of DDoS attacks, delivering scaling capacity. The platform also offers customized visibility into ongoing attacks.
Learn more about how to protect your website from bot attacks and bot management with the VMware NSX Advanced Load Balancer here.
For more on the actual implementation of load balancing, security applications and web application firewalls check out our Application Delivery How-To Videos.