Microsegmentation Definition
Microsegmentation is a security technique that enables security policies to be assigned to data center applications, down to the workload level. One major benefit of microsegmentation is that it integrates security directly into a virtualized workload without requiring a hardware-based firewall. This means that security policies can be synchronized with a virtual network. Policies can be synchronized with a virtual machine (VM), operating system (OS), or other virtual security targets. As a result, security models may be deployed deep inside a data center, using a virtualized, software-only approach.
Forrester Research established the concept of the “Zero Trust model” of virtualized network security. This model is a replacement to the “trust, but verify” model which was previously common. “Zero Trust” implements methods to localize and isolate threats, of which microsegmentation is an important component. Under “Zero Trust,” rules and policies can be assigned to workloads, VMs, or network connections. This means that only necessary actions and connections are enabled in a workload or application, blocking anything else.
Under the microsegmentation network security approach, security architects logically divide the data center into distinct security segments. These segments are defined down to the individual workload level. Architects may then define security controls and deliver services for each unique segment. Because security policies are applied to separate workloads, microsegmentation software can significantly bolster a company’s resistance to attack or intrusion.
What is Microsegmentation?
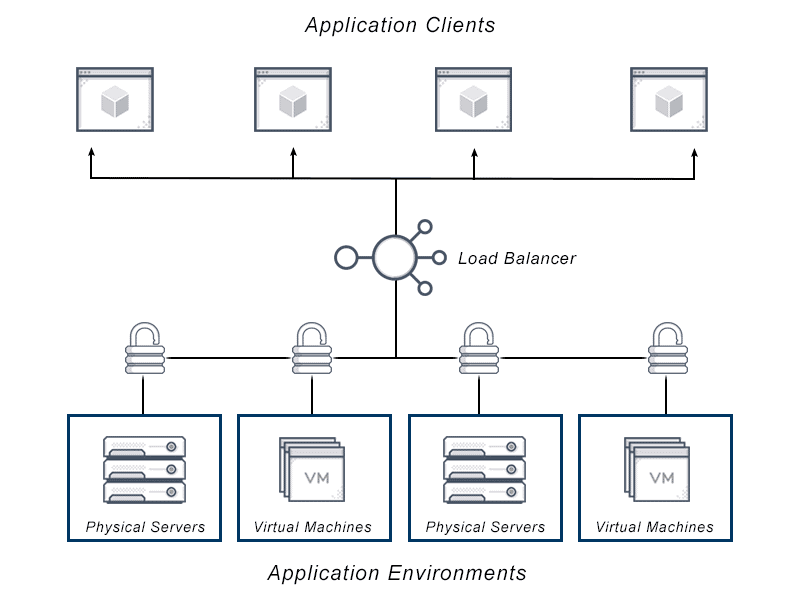
Microsegmentation is a security technique used in data centers and cloud network environments. This fine grained approach integrates security directly into a virtualized workload, removing the need for a firewall on the hardware. Security policies for access control may be synchronized with a virtual network. Virtual machines (VM), operating system (OS), or other virtual security targets can benefit from this policy approach. Through network segmentation, the attack surface and corresponding liability are minimized.
The “Zero Trust model” of virtualized network security was established by Forrester Research, as an alternative to “trust but verify.” This approach abolishes the idea of a trusted network inside a defined corporate perimeter for software defined networks and cloud deployments. “Zero Trust” mandates that enterprises create secure microperimeters of control around sensitive data assets. Encryption and authorized user identity are two common forms of microperimeters used in this model.
Under the microsegmentation network security approach, security architects divide the data center into distinct segments at the workload or application level. Architects may then define security controls and deliver services for each unique segment. Security policies applied to separate workloads through microsegmentation software significantly changes the attack surface.
This approach removes the need for multiple physical or hardware firewalls. This reduces manual effort involved in configuring internal firewalls for east-west traffic control. It also reduces the effort required to maintain those configurations over time. Those configurations often mount greater cost and complexity for the enterprise.
How Does Microsegmentation Work?
Network segmentation isn’t new. Enterprises have employed firewalls, virtual local area networks (VLAN) and access control lists (ACL) for their network segmentation security models.
Network segmentation breaks an Ethernet network into subnetworks (or subnets) which allow network traffic to be organized and contained. This approach boosts network performance and can introduce simple security in traditional static networks. The rise of software-defined networks and network virtualization has paved the way for microsegmentation.
Software-defined networking (SDN) and software-defined data center (SDDC) technologies have changed the data center landscape. They have catalyzed the ability for the policies to be applied to individual workloads to further reduce the attack surface.
Network microsegmentation uses virtualization technology to create increasingly fine grained secure zones in data centers and cloud deployments. These zones isolate each individual workload or application and secure it separately. The idea is to significantly reduce the exposed surface vulnerable to malicious activity. This restricts unwanted lateral (east west) traffic once a perimeter is penetrated.
Identity driven microsegmentation and encrypted microsegmentation both restrict lateral access within networks. Both approaches limit the permissions to the micro-packet or workload. Since policies are tied to logical segments, any migration of the workload or packet move the security policies along with it. This eliminates manual configuration processes which can lead to security flaws.
Why is Microsegmentation Important?
Microsegmentation is built for today’s security environments — and tomorrow’s. Cyberthreats are prolific and continuously adapting — hackers’ creativity reveals no shortage of tactics to do damage to enterprises of all kinds. Many argue that “Trust but verify” is no longer a valid security model. Moat and castle strategies ignore threats that compromise assets inside the castle.
Traditional firewalls can remain in place to enable security perimeter (north-south) defenses. Microsegmentation restricts unwanted communication between workloads (east west) traffic. This zero-trust security model addresses network attacks where attackers penetrate the perimeter and wait before deploying their ultimate disruption. This model is on the rise.
Many consider it necessary to assume your enterprise has already been compromised; you simply don’t know it yet. Those proponents argue that “Trust but verify” leaves enterprise leaders flatfooted and focused on crisis management instead of proactive network security. Zero Trust provides the proactive, architectural approach to align with mission priorities.
Microsegmentation does not eliminate the threat of cyberattacks, but reduces bad actors’ access to a small segment of the organization’s data. That can restrict the impact of a problematic incident.
For example, identity driven microsegmentation allows communities of interest to be provisioned with access quickly and efficiently. Administrators can then monitor and secure access control, to restrict permissions once the workload is complete. By enforcing segmentation with encryption at the workload or application level, security architects can hide sensitive packets.
If adversaries are able to infiltrate a microsegment, the damage would be contained to that small area. Intruders would be unable to move laterally and attack other segments. That interrupts the process by which an attack is escalated and could mean the difference between a manageable incident and an enterprise-wide catastrophe.
How to Implement Microsegmentation
Microsegmentation is widely regarded as a best-practice solution for securing data center and cloud assets. It is considered one of the first practices for implementing a “zero trust” security model. Microsegmentation policies dictate which applications can and cannot communicate with each other. Well-designed policies in this model ensure any unauthorized communication attempt is not only blocked. They can also trigger an alert that an intruder may be present.
Enterprises that successfully make the microsegmentation switch typically take a phased approach. This approach starts with a few “quick wins” on priority projects and gradually builds out a more robust program. In the process, the buy-in from this approach creates momentum which catalyzes policy roll-out across the whole enterprise.
Start by focusing on projects that are manageable, fairly easy to complete, and can deliver tangible results. Some common areas security architects prioritize are regulatory compliance, and devops. Security architects can then create secure data repositories for sensitive data types. Examples include those which may generate protected health or medical data.
These examples represent organizational needs for which microsegmentation is well-suited. They highlight the stakeholders who work outside the IT security team. Their buy-in is often required for an effective network microsegmentation strategy to work. Many organizations begin by convening all stakeholders to identify priorities and establish an implementation hierarchy.
Enterprise leaders may look to security to reach out to stakeholders from all business and IT units. The security team may be expected to take responsibility to ensure all stakeholders understand how all the application and business pieces work together. Thoughtful planning and mapping out the security model in advance will save hours of trial and error in implementation.
Creating effective and practical microsegmentation requires a thoughtful approach to implementation. Be clear on the essential process-level visibility. Equip all stakeholders with the information they need to identify logical groupings of applications for segmentation. Establish platform-agnostic policies so each packet or workload may be fully secure in heterogeneous environments, where they may migrate.
Label assets clearly to ensure that they can be closely-monitored in dynamic and auto-scale environments. Develop customizable hierarchies which reflect the importance of empowering different stakeholders. Give them the needed tools to organize and create rules that meet their workload or application’s unique needs. Develop a platform to automate policies and segments. This means that, as infrastructure and workload demand scales, newly deployed workloads can be appropriately allocated.
Microsegmentation Implementation Phases
Microsegmentation implementation can generally be broken down into six phases:
- Find and identify all the applications running in the data center. Ensure you understand the level and bandwidth of access control required.
- Define which applications need to be able to communicate with each other.
- Develop a hierarchy of logical groups for the creation of security policies. Use a careful definition to avoid creating too many discrete groupings or creating groups so broad that policies will lack precision.
- Once the logical groupings are defined, policies can be created, tested and refined for each group.
- Deploy policies across the workloads and applications prioritized for this implementation.
- The solution should enable monitoring of every port and all east-west traffic for anomalies.
What are the Benefits and Challenges of Microsegmentation?
Traditional firewalls can remain in place to maintain familiar perimeter (north-south) defenses. Microsegmentation significantly limits unwanted communication between workloads (east-west) within the enterprise. Microsegmentation allows direct east west communication between approved systems. This eliminates the need to hairpin traffic. Without hairpinning, network architects must maintain a simpler and higher-performing design.
Microsegmentation gives companies greater control over east west traffic or lateral communication that occurs between servers. Increasingly, this traffic bypasses perimeter-focused security tools. Bulkheading sensitive areas of the network away from less-valuable and less-hardened areas is a technique security architects use. They lean on segmentation to thwart attackers from moving laterally and escalating privileges across networks. Dark Reading estimates that 75% to 80% of enterprise traffic flows east-west, or server-to-server, between applications in today’s hybrid cloud world. Segmentation rules applied to the workload or application reduce the risk of an attacker moving from one compromised device to another.
Network virtualization and microsegmentation have the potential to provide boosts in network security because of the notion of persistence. In a physical network environment, networks are tied to specific hardware boxes. Security for this model is often implemented by a hardware-based firewall, which gates access by IP addresses or other security policies. If the physical environment is changed, these policies are ineffective.
In a virtual environment, architects can create secure policies assigned to virtual connections. Those policies and connections can move with an application if the network is reconfigured – making the security policy persistent. Many users like the fact that software-defined networking (SDN) supports moving workloads around a network quickly. In SDN microsegmentation the security policy gets assigned to the workload level. This means that the access control can persist no matter where the workload is moved.
Operational efficiency presents both a benefit and a challenge for the enterprise implementing microsegmentation. The traditional hardware or “trust but verify” approach demands a number of control tools which can get unwieldy. Things like access control lists, routing rules and firewall policies which can introduce a lot of management overhead.
These policies can be difficult to scale in rapidly changing environments. Microsegmentation is typically done in software, which makes it easier to define fine grained segments. On a software defined network, IT can work to centralize network microsegmentation policy and reduce the number of firewall rules needed.
On the other hand, consolidating firewall rules and access control lists and translating them into a new policy framework can be challenging. One important starting point is mapping the connections between workloads, applications, and environments to establish the proper policies. This requires institutional resources and buy-in.
Complexity and consistency are important to consider, and may present unexpected challenges for administrators implementing microsegmentation. Microsegmentation basically distributes security policies and rules to workloads.
Those policies and rules must follow consistent guidelines, and account for all workloads — even idle or powered-down virtual machines. Without guidelines or best practices, it’s possible for policies to shift between workloads or locations. Without a policy that closely monitors for complexity, an idle workload may come online in lockdown without the ability to communicate properly.
What types of Technology Insight for Microsegmentation are Required to Deploy Properly?
Research firm Gartner says microsegmentation is the future of modern data center and cloud security. However, they underscore the essential nature of getting the microsegmentation-supporting technology right. Choosing the wrong one can be analogous to building the wrong foundation for a building and trying to adapt afterward. In addition, microsegmentation, if not conducted properly, can lead to a security practice which creates new problems such as oversegmentation.
Gartner defines four different architectural models for microsegmentation. Native microsegmentation uses the inherent or included capabilities offered within the virtualization platform, IaaS, operating system, hypervisor or infrastructure. The third-party model for microsegmentation is based primarily upon the virtual firewalls offered by third-party firewall vendors. The overlay model for microsegmentation uses some form of agent or software within each host. This model is in contrast with moderating communications the way that firewalls do. The hybrid model of microsegmentation provides a combination of native and third-party controls.
In order to deploy this properly, stakeholders need to understand their network. Factors include what types of architecture will best suit their needs. They also need to know how that architectural model will connect with the network dependencies they must manage. Each stage of microsegmentation deployment requires an understanding of the enterprise’s network and dependencies within that network. Selecting the vendor, deploying and testing the policies requires an understanding of the architectural model, access requirements, and how they fit together.
What are some Microsegmentation Vendors?
When comparing products for microsegmentation in virtualized data centers, there are a number of different vendors to consider. Research firm Gartner defines four different architectural models for microsegmentation. The vendors in the microsegmentation market are grouped by their offerings along these architectural models.
Native microsegmentation uses the inherent or included capabilities offered within the virtualization platform, IaaS, operating system, hypervisor or infrastructure. Vendors include AWS microsegmentation, Microsoft and VMware microsegmentation. The third-party model for microsegmentation is based primarily upon the virtual firewalls offered by third-party firewall vendors. Vendors include those well-known for providing firewall solutions, such as Cisco, Checkpoint, Fortinet, Juniper, Palo Alto Networks, SonicWall, Sophos, and Huawei.
The overlay model for microsegmentation uses some form of agent or software within each host. This is in contrast to moderating communications the way that firewalls do. Vendors include CloudPassage, Drawbridge Networks, Guardicore microsegmentation, Illumio, Juniper, ShieldX, vArmour, and Unisys microsegmentation. The hybrid model of microsegmentation provides a combination of native and third-party controls.
Does VMware NSX Advanced Load Balancer, now Part of VMware, offer Solutions for Microsegmentation?
VMware NSX Advanced Load Balancer integrates into NSX with enhanced load balancing and WAF capabilities which work across multiple clouds and environments. NSX (via NCP) can apply microsegmentation to container pods with predefined tags based rules. NSX provides container clusters with full network traceability and visibility.
For Kubernetes microsegmentation, NSX (via NCP) can apply Kubernetes network policy per namespace. NSX has built-in operational tools for Kubernetes. Predefined tag rules enable you to define firewall policies in advance of deployment. These tag rules are based on business logic rather than using less efficient methods such as static IP addresses to craft security policy. With this method, security groups defined in NSX are microsegmented to protect sensitive applications and data down to the pod and container level.
For more on the actual implementation of load balancing, security applications and web application firewalls check out our Application Delivery How-To Videos.